What Is WiFi Security?
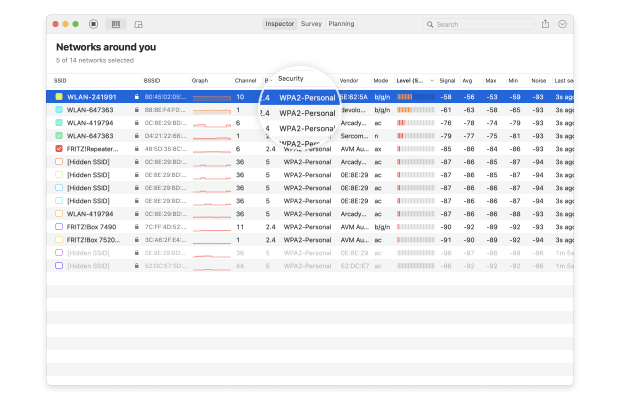
As you may know, WiFi networks transmit data between devices using radio waves, typically on the 2.4 gigahertz and 5 gigahertz radio-wave frequencies. Just like you can tune an FM radio to a specific channel to listen to your favorite radio show, anyone with the necessary skills can configure a WiFi capture device to collect all data that’s transmitted on a specific frequency.
To prevent potentially malicious strangers from seeing what you do online, stealing your passwords, and doing all kinds of other things, modern devices implement several different wireless network security standards, whose purpose is to encrypt wirelessly transmitted data and turn it into meaningless ciphertext.
Thanks to WiFi security, you can connect to a public WiFi network at an airport together with hundreds of other people and know that your personal information will remain private.
What Is a Network Security Key for WiFi?
Secure WiFi connections are established when wireless clients (smartphones, laptops, etc.) and the wireless networks they connect to prove their identities to each other.
From the point of view of a regular user, the authentication process begins with the network security key prompt. This prompt acts as a gate, preventing those who don’t have the right network security key from establishing a secure connection.

Network security keys are typically alphanumerical passwords, but passwordless authentication using technologies like Wi-Fi Protected Setup (WPS) is also possible.